INTRODUCTION:
In today’s digital world, almost every person is highly dependent on the internet, and most daily activities are now carried out online. One of the most important tools that has emerged from this digital transformation is the credit card, which has become an essential part of the modern financial system.
A credit card allows people to make quick and convenient purchases without using cash. It is a type of payment card issued by banks that enables users to borrow money digitally for transactions and repay it later. This makes credit cards especially useful in emergency situations when a person does not have immediate cash but needs to make a payment or access a service.
The concept of credit cards began in the mid-20th century. In the early days, transactions were handled using simple paper-based systems and later magnetic stripe technology, which were not very fast or secure. However, with the advancement of technology, credit cards have evolved into highly secure financial tools, now featuring EMV chips and contactless payment systems.
Today, credit cards play a crucial role in global commerce by making transactions faster, more efficient, and widely accessible to people around the world.

TECHNOLOGY:
EMV Chip Technology
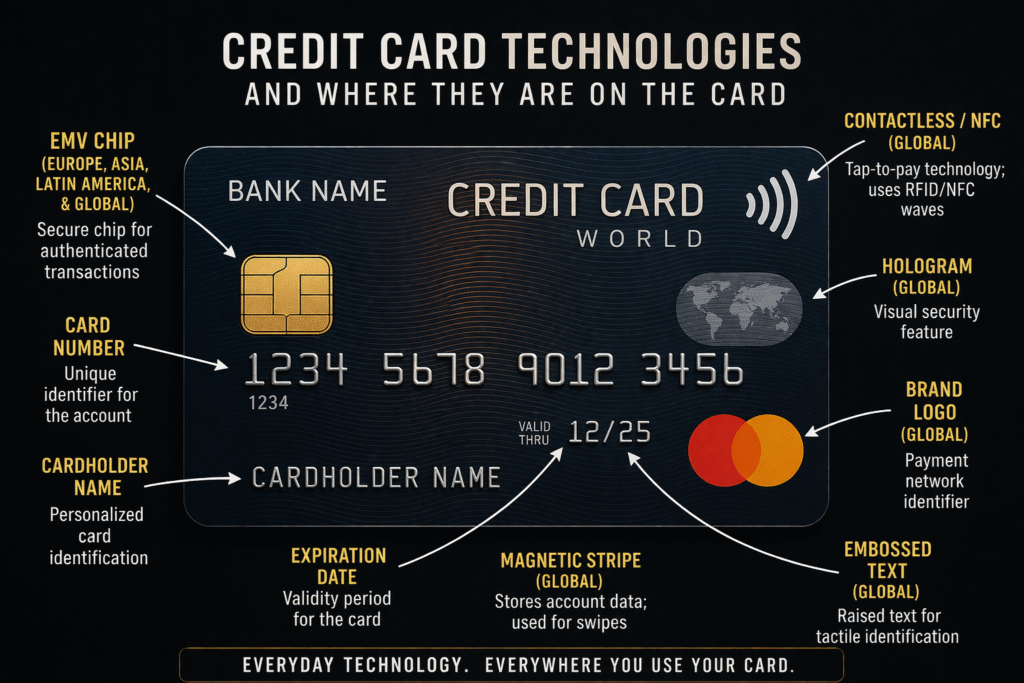
There are many technologies used in credit cards that make transactions secure and fast. One of the most important technologies is the EMV chip. In this system, a small microchip is embedded in the card, which securely stores encrypted data and generates a unique code for every transaction.
This dynamic code changes each time the card is used, making it extremely difficult for fraudsters to copy or duplicate the card information. As a result, EMV technology has significantly reduced credit card fraud and improved the overall security of digital payments. It is considered a major advancement in the evolution of modern payment systems.
Magnetic Stripe Technology
Earlier, credit cards used magnetic stripe technology, where card information was stored on a black strip at the back of the card. During a transaction, this data was read by swiping the card through a machine.
However, this method was less secure because the stored data was static and could be easily copied using simple devices. This led to an increase in fraud cases, as criminals could duplicate card information and misuse it.
Due to these security weaknesses, magnetic stripe technology is now being gradually replaced by more advanced and secure chip-based systems like EMV.
NFC (Contactless Payment Technology)
Another key technology used in modern credit cards is Near Field Communication (NFC), which makes transactions faster and more efficient. It enables contactless payments, allowing users to simply tap their card on a payment terminal to complete a transaction within seconds.
NFC works by using short-range radio signals to establish communication between the card and the payment device. Because this communication occurs over a very small distance, it is both quick and secure. This eliminates the need to swipe or insert the card, significantly improving convenience for users.
Along with speed and ease of use, NFC technology also incorporates strong security features, making it a reliable and widely adopted solution in today’s digital payment ecosystem.
Encryption Technology
In modern credit cards, encryption technology plays a crucial role in ensuring user safety. It converts sensitive user information into a secure coded format, making the data unreadable to unauthorized users.
Each transaction uses encrypted data that is unique to the user, which adds an extra layer of protection. This ensures that even if the data is intercepted, it cannot be easily accessed or misused.
As a result, encryption significantly enhances the security of credit card transactions and has helped reduce the number of fraud cases, making digital payments safer and more reliable.
Tokenization Technology
Another important security technology used in credit cards is tokenization. It adds an extra layer of protection by replacing the actual card details with a temporary, unique code (called a token) during each transaction.
Instead of transmitting the real card number over the network, the system uses this token, which has no meaningful value if intercepted. Additionally, a new token is often generated for every transaction, further enhancing security.
This approach helps protect the user’s sensitive card information from being exposed online and significantly reduces the risk of fraud in digital payments.
TRANSACTION:
Card Usage
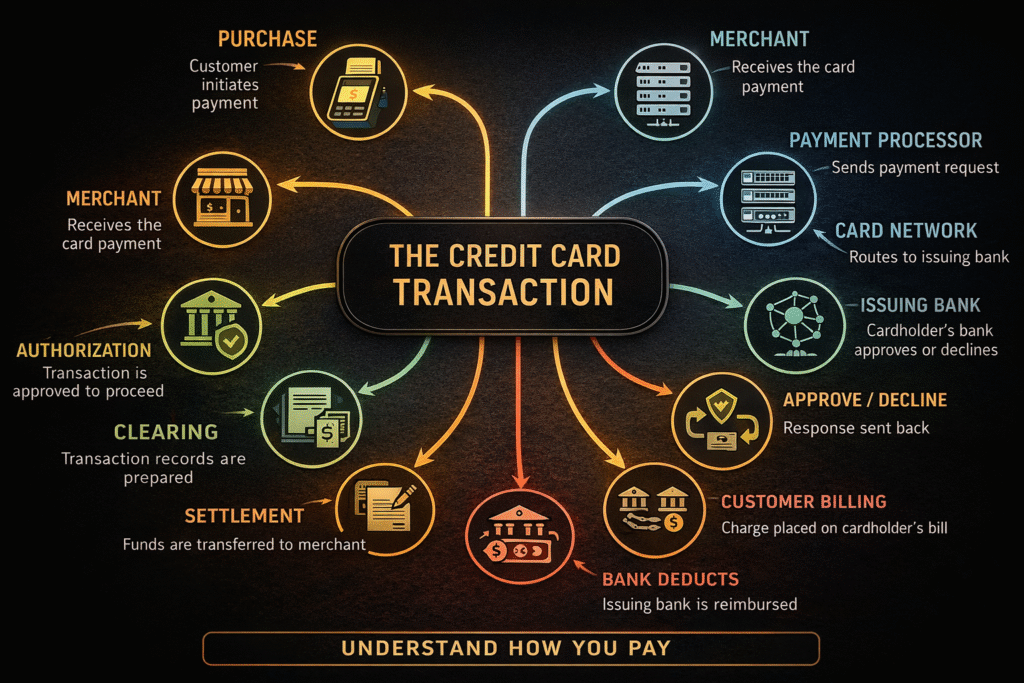
Now, let’s understand how a credit card transaction works, especially for new users. The process begins when a user swipes, inserts, or taps their card on a payment terminal.
The terminal then reads the card information using the available technology—either the EMV chip, magnetic stripe, or NFC (for contactless payments), depending on the type of card and machine.
Once the card details are read, the payment system processes the information securely and initiates the transaction. This entire process happens within seconds, making credit card payments fast, simple, and convenient for users.
Data Transmission
Once the payment terminal captures the user’s card details, it sends the transaction information—such as the card number and transaction amount—to the acquiring bank through a secure payment network.
This network is specially designed for financial transactions and uses advanced security measures to protect the data from fraud or unauthorized access. The information is transmitted in an encrypted form, ensuring that sensitive user details remain safe during the process.
This step happens almost instantly and is a crucial part of ensuring that the transaction is both secure and reliable.
Payment Network Processing
After receiving the transaction details, the acquiring bank processes the request and forwards it to the payment network, such as Visa or Mastercard.
The payment network then routes the transaction to the issuing bank (the bank that issued the user’s credit card) for verification. This step ensures that the request reaches the correct bank securely and efficiently.
This entire process happens within seconds and is essential for confirming whether the transaction can be approved or not.
Bank Verification
The issuing bank then verifies the transaction by checking several important details, such as the card’s validity, the available credit limit, and user authentication methods like a PIN or OTP.
This step ensures that the transaction is legitimate and that the cardholder has authorized the payment. It also helps detect any suspicious activity,
Approval or Rejection
After the verification process, the issuing bank sends an approval or rejection message back through the same secure network to the payment terminal within a few seconds.
If the transaction is approved, the payment is successfully completed, and the amount is reserved from the cardholder’s credit limit. The funds are then transferred from the buyer’s card account to the seller’s account through the banking system.
This entire process happens quickly and seamlessly, ensuring that both the customer and the merchant experience a smooth and reliable transaction.
Transaction Completion
Once the transaction is approved, the payment is processed successfully, and the amount is deducted from the user’s available credit limit. The user receives a confirmation of the transaction, while the merchant is assured that the payment has been successfully completed.
FRAUD PREVENTION TECHNOLOGIES:
One-Time Password
For online transactions, One-Time Passwords (OTP) play an essential role in security. An OTP is sent to the user’s registered mobile number or email during the transaction process.
This ensures that only the authorized user can complete the payment, as the OTP must be entered to verify the transaction. By adding this extra layer of authentication, OTP significantly enhances security and helps prevent unauthorized access or fraud.
Artificial Intelligence Fraud Detection
Artificial Intelligence is also widely used in credit card transactions to monitor user behaviour and transaction patterns. It continuously analyzes how a user typically spends and identifies any unusual activity.
If something suspicious occurs—such as a sudden high-value purchase or a transaction from an unusual location—the system can quickly detect it. In such cases, the transaction may be automatically flagged or even temporarily blocked for security verification.
This intelligent monitoring system helps prevent fraud in real time and adds an advanced layer of protection to digital payment systems.
Transaction Alerts
Users also receive instant notifications through SMS or mobile apps for every transaction. This real-time alert system helps users quickly identify and report any unauthorized activity.
By being immediately informed, users can take prompt action—such as blocking their card or contacting the bank—before any major loss occurs. This feature plays a key role in preventing fraud and enhancing overall transaction security.
Two-Factor Authentication
Another common security method used in credit card transactions is two-factor authentication (2FA). This method requires two types of verification, such as a PIN or password and a one-time password (OTP).
By adding this extra layer of security, two-factor authentication ensures that even if one piece of information is compromised, the transaction cannot be completed without the second verification. This significantly reduces the risk of fraud.
At the same time, the process remains quick and user-friendly, providing both strong security and convenience for users.
CONCLUSION:
In conclusion, credit cards have become an essential part of modern digital payment systems. They provide convenience and financial flexibility, especially for middle-class users, allowing them to make important or desired purchases even when immediate funds are not available.
Powered by advanced technologies such as EMV chips, encryption, and fraud detection systems, credit cards ensure secure and efficient transactions. These technologies work together to provide both safety and ease of use in everyday payments.
However, responsible usage and continuous improvement in security systems are crucial to minimizing risks and shaping a safer and more reliable future for digital payments.
KNOW MORE:
INTERNAL LINKS:
https://techman.live/wp-admin/post.php?post=329&action=edit
https://techman.live/wp-admin/post.php?post=322&action=edit
EXTERNAL LINKS:

